In the Fast-Paced World of Financial Cybersecurity, Why Some Technologists Recommend Taking It Slow
Industry and Academic Experts Share Insights into Changing Security Landscape at Stevens' Annual Conference
Today’s treasure chest of consumer data may be tomorrow’s Pandora’s box.
That was the takeaway from a Stevens Institute of Technology-hosted conference on financial cybersecurity that featured a group of industry experts who shared their perspectives on the data and its role in this discipline.
“You have to pick a position and present a roadmap for how you plan to use and analyze data, and get that validated proactively,” said Tom Doughty, vice president and chief information security officer at Prudential Financial. “If you try to construct that roadmap after the fact, it will probably be met with much less cooperation.”
Doughty shared his own experiences promoting a more disciplined approach to data collection for Prudential during his presentation at FinCyberSec 2019. Organized by Dr. Paul Rohmeyer, associate teaching professor of Information Systems at the School of Business, in conjunction with the New Jersey chapter of ISACA, the annual conference explores the threats, challenges and opportunities facing financial institutions and service providers in the cybersecurity space.
The goal of FinCyberSec, Dr. Rohmeyer said, is to promote knowledge sharing about cybersecurity challenges in financial systems among both industry and scholarly audiences. “This year’s conference had higher student participation than prior years, adding to great discussion and also presenting industry networking opportunities for our students,” he said.
Many of the most pressing issues for these firms are questions surrounding the idea of digital ethics and how to balance a duty to monitor for threats with the imperative to protect the privacy of users and employees. As Doughty put it, when it comes to data collection, “can does not equal should.” He hazarded against “rushing headlong” into new technologies without first thinking through their use cases.
“The idea of maintaining some altitude can be difficult for most technologists,” he said, “but it’s OK, once in a while, to have technology that isn’t being used to its full potential until you really understand it. There’s no going back once it’s been unleashed, so it’s up to companies to make responsible decisions.”
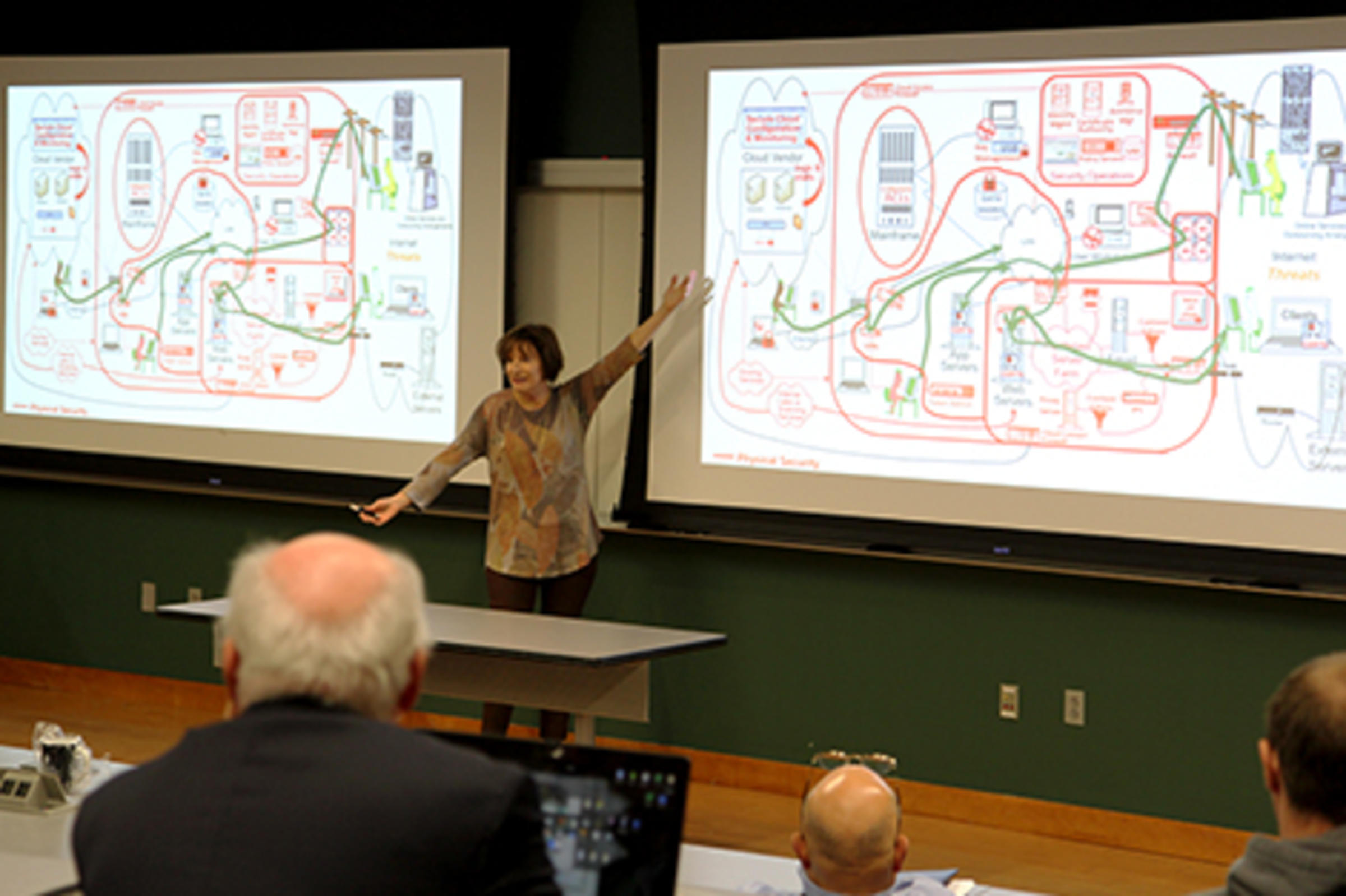
That point was reinforced during a presentation on the history of cybersecurity technology from FrameCyber’s Jennifer Bayuk M.S. ’92 Ph.D. ’12, an expert with more than 25 years’ experience in information security management and IT due diligence. Bayuk is also a respected alumna who worked as director of the Cybersecurity program while pursuing her doctoral degree in Systems Engineering. During the conference, she said taking a systems engineering perspective can be illuminating at times.
“If you look at how we got to this point in security technology, you remind yourself what the system as a whole looks like, and the research problems jump out at you,” she said.
It’s a regular theme of research and teaching at the School of Business — that the systemic nature of modern enterprises creates many new opportunities for collaboration, customer engagement and so on, but also opens up new avenues of attack.
While Bayuk reflected on cybersecurity’s past, Aman Singh, chief scientist at Palindrome Technologies, looked to its future. He capped off the conference with his presentation highlighting technical architecture considerations, the vulnerability landscape for web-based applications, recent breach events and his current research on the internet of things.
Information Systems Program Business Intelligence & Analytics degree School of Business