Master's in Financial Engineering
Bring a quantitative approach to the complex technical challenges facing the finance industry, ensuring you can create value throughout your career.
Program Highlights
The Confluence of Math and Business: The masters in Financial Engineering program originated in Stevens’ mathematics department and continues to uphold a high standard of mathematical rigor. With its relocation in 2018, our graduates have become even more valuable employees. By also being fluent in the language of business they can identify new opportunities and drive more strategic decision-making.
Customizable Program: Students can customize their Financial Engineering program to their career goals and pursue a specialization in investment banking and valuation, financial analytics and risk, wealth management or certified financial planning. Our courses and curriculum are constantly updated to ensure the most relevant skills and information are taught.
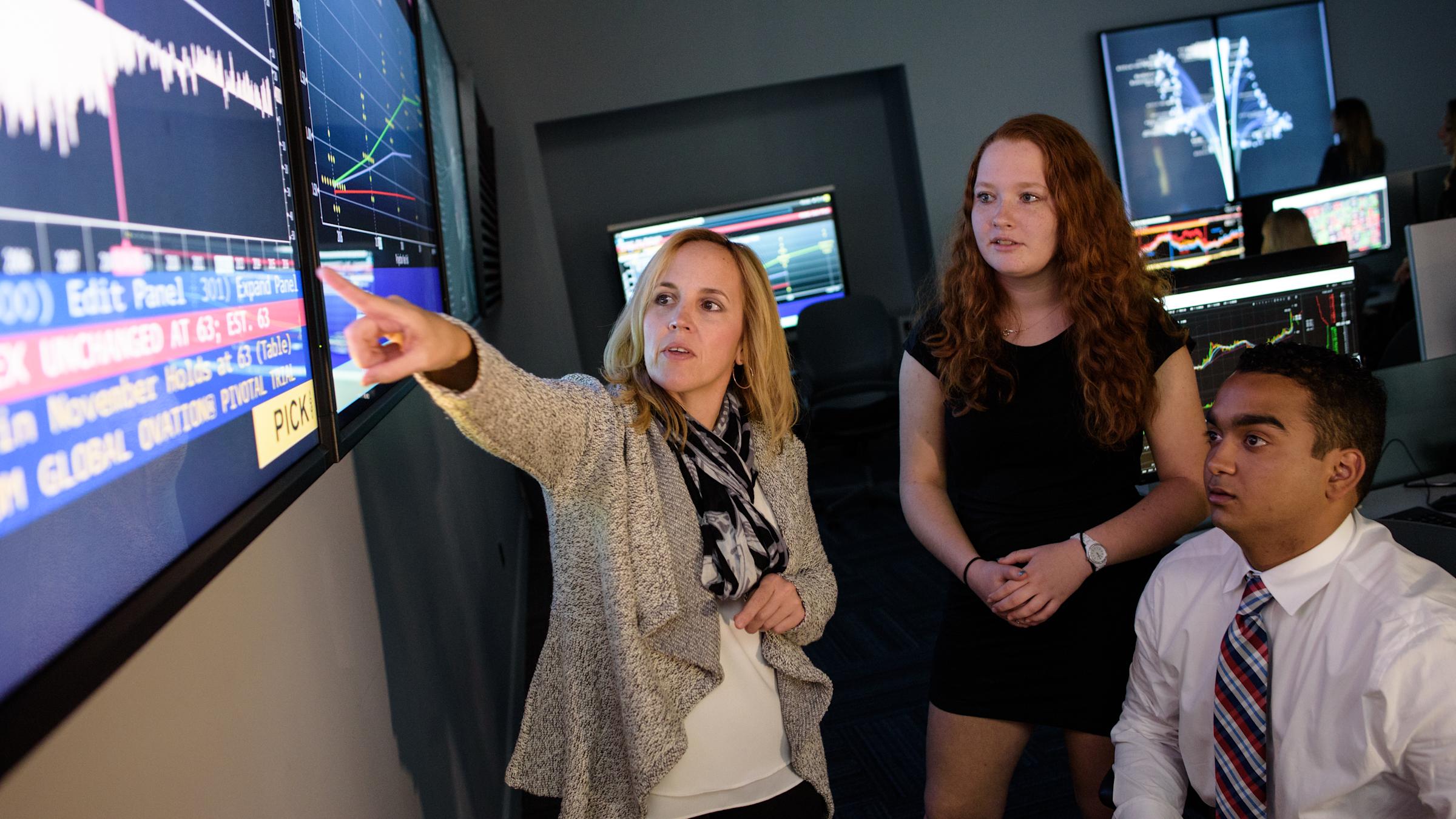
Wall Street Tools: Students gain hands-on experience with the latest technologies used by Wall Street firms and global financial institutions, providing them with a competitive edge in the job market. The program's emphasis on practical application ensures seamless integration into dynamic finance roles.
The Heart of Global Finance: Located so close to the financial capital of the world, New York City, Stevens provides students with unparalleled access to industry leaders, networking events and real-world finance experiences. Our strategic location offers a competitive advantage for students seeking to launch successful careers in the heart of global finance.
Forging the Future of Fintech: A collaboration between Stevens and Rensselaer Institute of Technology (RPI), The Center for Research toward Advancing Financial Technologies (CRAFT) was the first fintech-focused Industry University Cooperative Research Center (IUCRC) funded by the National Science Foundation. The Center offers students an amazing opportunity to delve into research in the rapidly evolving world of financial technology and to network with other academics and industry professionals.
Meta-Learning for a Competitive Edge: Develop invaluable meta-learning skills through our innovative curriculum, including the FE800 course, which fosters research abilities, communication prowess and interest in result-oriented techniques. By mastering the art of breaking down complex issues swiftly to create data-driven solutions, and gaining insights into thinking processes, attitudes, motivation, and decision-making contexts, you'll cultivate a meta-learning mindset that has become increasingly crucial in the digital era.
GMAT/GRE test scores are optional for all master’s programs. Applicants who think that their test scores reflect their potential for success in graduate school may submit scores for consideration.
Preparing the Next Generation of Financial Leaders
The finance world's rapid transition to a digital discipline has created incredible opportunities for experts in computer science, statistics, economics and mathematics to develop solutions to increasingly complex problems, such as how to value an asset, how to assess risk and the smartest ways to manage a portfolio. Quants are some of the most sought-after professionals on Wall Street for their coding versatility and ability to model financial data to drive better decision-making.
The Financial Engineering program at Stevens resides in the School of Business, giving it a practical orientation that few other programs offer. Lessons emphasize how technical tools can address specific challenges in the markets, while preparing you to identify inefficiencies, recognize opportunities and develop innovative new products. The Stevens program also recognizes the systemic nature of financial markets and prepares you for the challenges of working in large, interconnected environments.
The Financial Engineering program at the School of Business ranked #19 in QuantNet's 2026 Best Financial Engineering Masters programs in the United States. Our program also has the lowest private university tuition cost and is one of the lowest overall tuition, making it an affordable investment in your future. The 2026 QuantNet ranking is the most authoritative and comprehensive ranking of best Financial Engineering programs in the United States.
The Financial Engineering master's program at Stevens is available on campus or fully online.
Capstone Experience
No graduate business education is complete without an opportunity to apply what you've learned on a project of consequence. At Stevens, that takes many forms — a consulting assignment with an industry partner, a research project that addresses an industry need, even the chance to nurture your own entrepreneurial venture — and is customized for you, your education and your career aspirations.
Financial Engineering Careers
Derivative Analyst
Complex Securities Manager
Credit Algorithmic Quant
Credit Analyst
Quant Risk Analyst
EFX Trader
Options Surveillance Analyst
Quant Developer
Algorithmic Trading Modeler
Desk Strategist
Organizations hiring Financial Engineering graduates include companies such as: Bank of America, Citadel, Citigroup, Goldman Sachs, JPMorgan Chase, Morgan Stanley, UBS, Capital One, Deloitte, Intuit, Metlife, New York Life Insurance Company, New York Stock Exchange and more.
Earn Your Financial Engineering Master's Degree Just Minutes from NYC
Being minutes from Wall Street gives Stevens Financial Engineering students an unparalleled advantage in the world of investment banking, hedge funds and fintech innovation. This proximity to New York City provides direct access to top financial firms like Goldman Sachs, JPMorgan Chase, Morgan Stanley and Citadel, creating exceptional opportunities for internships, networking and full-time job placements. Students benefit from guest lectures, executive panels and hands-on learning experiences that immerse them in real-world finance tools, AI-driven trading and quantitative risk analytics. Additionally, Stevens' location places students at the center of fintech and AI-powered financial innovation, connecting them with blockchain startups, algorithmic trading firms and high-frequency trading platforms. With many Wall Street firms actively recruiting from local financial engineering programs, Stevens graduates gain a competitive edge in securing high-impact roles in global finance.
Admission Criteria
The master’s in Financial Engineering offers professionals a cutting-edge blend of applied mathematics, computational techniques and statistical analyses, combined with basic financial and economic theory. Because of the highly technical nature of a financial engineer's work, students are required to have an academic or professional background that prepares them to excel in such an environment.
Academic Transcripts
Your application must include official transcripts from all universities you have attended. These records must show your name, the name of the university attended, enrollment dates, coursework completed, and grades assigned.
Interviews
Stevens often invites master's candidates to interview prior to making an admissions decision. If you are selected for an interview after submitting your application, you will receive instructions via email.
Letters of Recommendation
Your application must include two letters of recommendation. The strongest applications will include one letter from a current supervisor, and one from a former supervisor or previous employer who can speak to your leadership potential and discuss your professional performance.
Professional Resume
You must include a résumé with your application that highlights:
Academic record
Work and internship experience
Leadership abilities
Required coursework
Required coursework
Given the technical nature of this degree, students are required to have completed courses in each of the following disciplines prior to starting the program:
Calculus and differential equations.
Probability and statistics.
Linear algebra.
Programming (Java, C++, R or Python).
Stevens noncredit courses in these disciplines for students needing to satisfy these requirements.
Application Deadlines
APPLICANT | FALL | SPRING | SUMMER (Domestic Applicants Only) |
|---|---|---|---|
Master's Full-Time | April 15 | November 1 | May 1 |
Master's Part-Time | August 15 | January 1 | May 1 |
Graduate programs admit students on a "rolling" basis, meaning that students may still apply after the preferred deadlines.
Students requiring an F1 Visa are strongly encouraged to apply by the preferred deadlines to allow time for visa processing.
GMAT/GRE test scores are optional for all master’s programs. Applicants who think that their test scores reflect their potential for success in graduate school may submit scores for consideration.
Core Curriculum
The quantitative and systems-intensive perspective of the master's program prepares students to use financial engineering techniques to solve problems in securities valuation, risk management, portfolio structuring and regulatory concerns, with an emphasis on stochastic modeling, optimization and simulation techniques. The 30-credit degree includes six required courses that emphasize quantitative finance, financial services analytics, financial risk and regulation, and financial systems. As part of the degree, students are encouraged to take an integrated four-course certificate that allows for additional expertise in a particular discipline of their choosing.
FE 610 Stochastic Calculus for Financial Engineers - 3 Credits
This course provides the mathematical foundation for understanding modern financial theory. It includes topics such as basic probability, random variables, discrete continuous distributions, random processes, Brownian motion and an introduction to Ito’s calculus. Applications to financial instruments are discussed throughout the course.
FE 620 Pricing and Hedging - 3 Credits
This course deals with basic financial derivatives theory, arbitrage, hedging and risk. The theory discusses Ito’s lemma, the diffusion equation and parabolic partial differential equations, and the Black-Scholes model and formulae. The course includes applications of asset price random walks, the log-normal distribution and estimating volatility from historic data. Numerical techniques, such as finite difference and binomial methods, are used to value options for practical examples. Financial information and software packages available on the Internet are used for modeling and analysis.
FE 621 Computational Methods in Finance - 3 Credits
This course provides computational tools used in industry by the modern financial analyst. The current financial models and algorithms are further studied and numerically analyzed using regression and time series analysis, decision methods, and simulation techniques. The results are applied to forecasting involving asset pricing, hedging, portfolio and risk assessment, some portfolio and risk management models, investment strategies, and other relevant financial problems. Emphasis will be placed on using modern software.
FE 630 Portfolio Theory and Applications - 3 Credits
This course introduces the modern portfolio theory and optimal portfolio selection using optimization techniques, such as linear programming. Topics include contingent investment decisions, deferral options, combination options, and mergers and acquisitions. The course introduces various concepts of financial risk measures.
FE 680 Advanced Derivatives - 3 Credits
This course deals with fixed-income securities and interest-rate sensitive instruments. Topics include term structure of interest rates, treasury securities, strips, swaps, swaptions, one-factor and two-factor interest rate models, Heath-Jarrow-Merton (HJM) models, and credit derivatives — credit default swaps, collateralized debt obligations, and mortgage-backed securities.
FE 800 Project in Financial Engineering - 3 Credits
This course is designed for FE students undertaking a research or a project in financial engineering either individually or as a group. The project may be suggested either by faculty members or industry senior managers associated with your internship, as well as any internship that a student may receive through this course. The goal of this course is to involve students in developing research skills, communication skills while keeping their interest in result-oriented techniques. The ability to work on a research-oriented project in a group environment and train their professional presentation and scientific writing skills lead to a competitive graduate who is ready to lead in the work place.
Financial Engineering Electives & Certificates
In addition to the six core courses above, students need to complete four additional elective classes for a total of 12 credits. Those 12 credits may be any courses the advisor approves. In particular, students may choose to complete the elective courses from one of the following graduate certificate programs. This would allow students to graduate with a master’s degree and a graduate certificate at the same time.
Algorithmic Trading Strategies
This concentration emphasizes the design and implementation of financial trading systems in dynamic markets, with special focus on how software and automated decision support systems play roles in trading strategies. To complete this concentration, students must take the following courses:
Financial Analytics
The Financial Analytics concentration emphasizes statistical learning methods and database skills, preparing students to develop tools to manage enterprise-level challenges. Students apply data-driven solutions to complex financial problems in preparation for an industry in increasing need of such skills. To complete this concentration, students must take the following courses:
Financial Risk Engineering
Technology’s impact on market fundamentals means managers must understand the financial system, its environment and the risk measures that help quantify risk in its multiple hierarchies. Courses in this concentration emphasize a blend of technology and business to help graduates see the financial landscape from a systemic perspective, and to analyze and manage risk efficiently. To complete this concentration, students must take the following courses:
Students also complete an additional elective with advisor permission.
Financial Statistics
Proper statistical analysis, supported by new technology tools, helps managers assess markets and build products to create competitive advantages for the enterprise. This concentration gives students insight into technology-driven opportunities in finance through advanced data analytics. To complete this concentration, students must take the following courses:
Financial Computing
This concentration goes beyond basic programming and computing skills to teach students to use quantitative models to manage large financial data sets. Students learn financial computing models, financial databases, financial engineering software and specialized programming languages. To complete this concentration, students must take the following courses:
FE 505 Financial Lab: Technical Writing in Finance (1 credit)
FE 511 Introduction to Bloomberg and Thomson Reuters (1-credit lab)
FE 699 Project in Financial Computing (2 credits)
Students also complete an additional elective with advisor permission.
Meet the Program Director
Dr. Emmanuel Hatzakis director of the Finance and Financial Engineering programs, joined Stevens School of Business after a long career at Bank of America, UBS, Goldman Sachs and Merrill Lynch. His teaching curriculum focuses on wealth management, financial derivatives and fintech. He has a master's and Ph.D. from the Wharton School of the University of Pennsylvania.
Frequently Asked Questions (FAQs)
You may recognize this program as...
MSFE
Mathematical Finance
Finance and Risk Engineering
Risk management and Financial Engineering
Financial Engineering and Risk Management
Risk Engineering
Financial Risk Management
Quantitative Risk Management
Financial Mathematics
Engineering in Finance
Quantitative Finance
Computational Finance
Financial Systems Engineering
Quant Finance
Applied Financial Engineering
Financial Technology and Engineering
Data Science for Finance
What is financial engineering?
Financial Engineering is the practice of using mathematical models and computational techniques to solve complex financial problems. This graduate program focuses on risk management, derivative pricing and quantitative finance, preparing students to work in highly technical areas of finance.
Graduates are trained to create innovative financial products, manage risk and optimize financial performance using advanced quantitative methods.
What do financial engineers do?
Financial Engineering graduates excel in roles such as quantitative analysts, risk managers or financial engineers. They regularly use mathematical models to analyze financial markets, develop pricing models for complex financial products and manage risk.
Their ability to apply quantitative techniques to real-world financial problems makes them essential for investment banks, hedge funds and other financial institutions that require advanced technical expertise.
What makes this program different from a Master's in Finance?
A Master’s in Finance focuses on traditional financial principles, while Financial Engineering integrates advanced math, AI, machine learning and quantitative modeling to solve complex financial problems.
Can I work while completing this program?
Yes! The program offers part-time flexibility, allowing professionals to balance work, study and internships.
What industries hire Financial Engineering graduates?
Stevens graduates work in:
Investment Banking
Hedge Funds
Fintech
Risk Management
Corporate Finance
Why choose Stevens for financial engineering?
Top-Ranked & Industry-Recognized
STEM-Designated for Career Growth
Customizable Specializations:
Algorithmic Trading Strategies
Financial Analytics
Financial Computing
Financial Risk Engineering
Financial Statistics
Competitive Tuition & High ROI
GMAT/GRE Optional
Is there a certification program for financial engineering?
While there is no single universal certification for financial engineering, professionals often pursue the CFA, FRM or CQF designations. Stevens offers a master's degree in Financial Engineering that provides comprehensive training in this specialized field.