Stevens professor’s innovative research improves cybersecurity and data privacy in the world of wireless information transmission and storage
In the early days of data management — when information was kept in cardboard boxes or, later, on desktop computers and onsite data storage systems — putting a sturdy lock on a door to secure these areas containing sensitive information was enough to significantly minimize the potential for theft and invasion of privacy.
Today, however, as more and more organizations and individuals outsource their data storage to Internet-based servers known as clouds, that online data and its remote home are increasingly vulnerable to cyberattacks. Shucheng Yu, associate professor of electrical and computer engineering at Stevens Institute of Technology, was one of the first trailblazers working to thwart such malicious acts and keep the cloud a safer place both for cloud service providers and for users of these virtual storage facilities.
“Around 15 years ago, when the concept of cloud computing was new and users were starting to send all their data to these remote cloud servers, I saw it as an interesting computing paradigm with very real security implications,” recalled Yu, who also leads the Stevens AISecLab, which conducts interdisciplinary research and industry collaborations to address complex analytics and information security issues.
“I was among the early advocators and researchers looking at this situation,” he said. “I still remember presenting a paper at a conference in 2010, and when I said we could not fully trust the security of cloud servers, people challenged me. Then, 10 years later, it was clear that this threat was a reality, and now everybody recognizes that remotely stored data should be protected.”
Yu’s solution for data security, which he continues to develop, supports the current gold standard of end-to-end data encryption, but then goes a step further to harness the cloud itself to provide an additional layer of protection.
“If you have an iPhone, for example, and you use iCloud to synchronize and store your photos, without some kind of security, those photos are subject to data breaches,” he explained. “But with encryption, your phone converts those photos into code, generates a key and sends that concealed data to the cloud. Even if hackers steal the data from the cloud server, the data will still be encrypted. But the key is stored in your phone, so you can see the data whenever you want.”
The challenge of breaking that code becomes even more difficult with the addition of Yu’s creative approach.
“We have the cloud do computations over the encrypted data to more strongly secure that data,” he said. “The cloud doesn’t know what the content is, but it participates in the computation. It’s very effective, and you, as the user, don’t have to do anything.”
Papers Yu has published or co-published on this topic have been cited more than 10,000 times. As quantum computing continues to advance, Yu is also beginning to investigate cloud data security against potential quantum attacks and to develop relevant cloud data security solutions.
Billions of devices, one goal: Wireless security
At the same time, wireless devices and Internet of Things (IoT) technologies continue to weave themselves into our daily lives, bringing with them a broad range of security risks. Cyber attacks can impact a single device and can include listening in on private communications, impersonating devices or jamming signals. They can also become more complex, affecting entire wirelessly connected systems, such as vehicular networks, drones, power systems and smart homes. Beyond passively harvesting sensitive information, hackers can inject malicious signals to disrupt the system’s operation entirely.
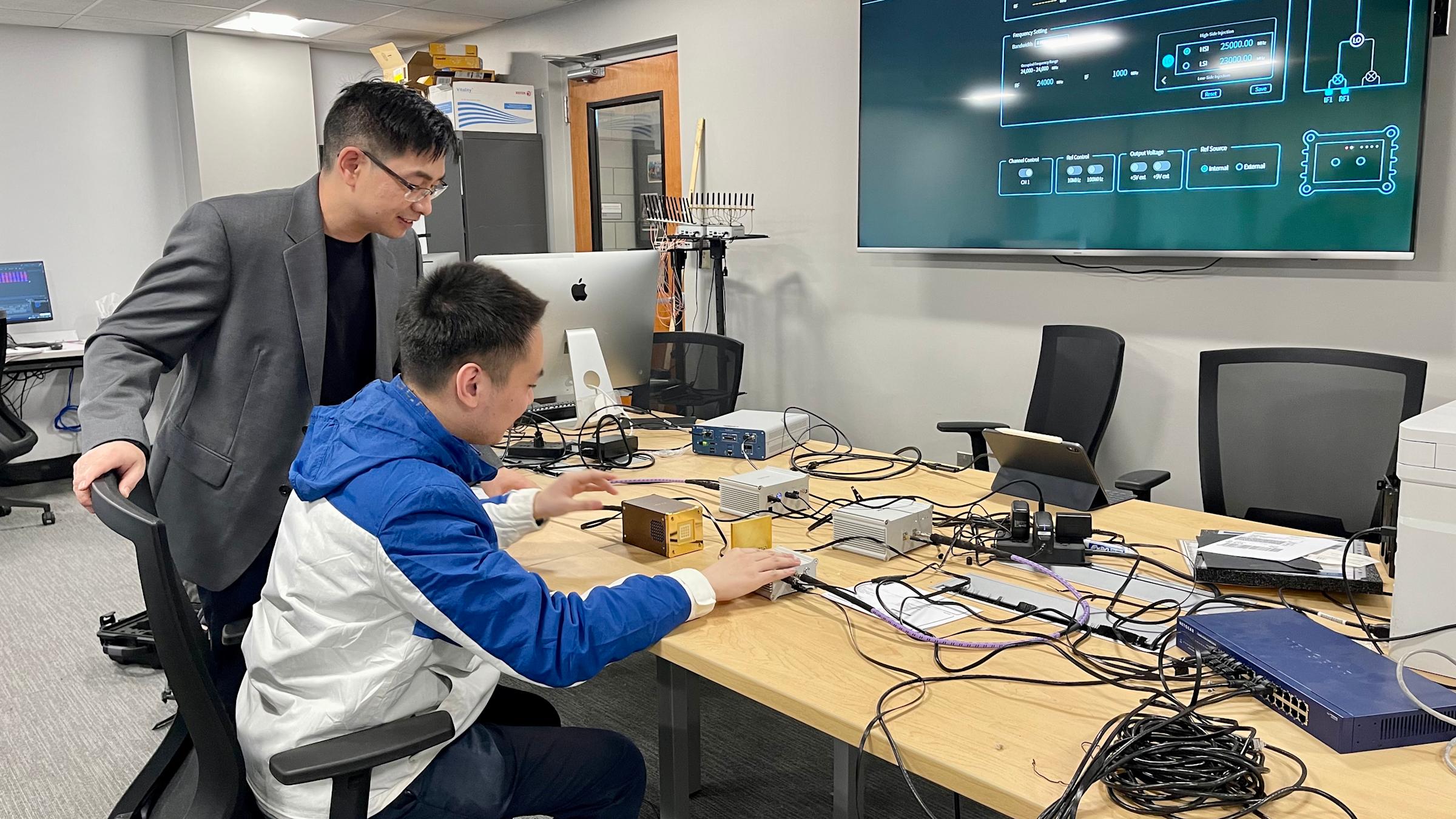
Yu is fighting back with a focus on the fundamental problem of securing IoT environments powered by 5G and nextG techniques from the physical layer.
“Some solutions require the user to plug the device into special hardware, scan it or otherwise get involved in securing it, which is not reliable,” Yu said. “These devices talk to each other over wireless transmissions, which is open to eavesdropping and hijacking. The problem becomes further complicated because we are talking about the Internet of Things: billions of devices around the world that are wirelessly connected but not always compatible with each other in hardware and software.”
In response to such vulnerabilities, Yu is exploring using the physical properties of radio frequency signals, which are available to all wireless devices, as part of the solution.
“We’re looking at the secret wireless fingerprints that can be extracted from RF signals transmitted and received by wireless devices,” he said. “We want to ensure the encryption is secure, lightweight, ubiquitously compatible across wireless devices, easily deployed and intuitive for all users.”
Focus on the journey
The National Science Foundation has funded three of Yu’s research projects related to wireless security, as well as several other projects related to cloud data services. In addition, Yu was recognized with the Test of Time paper award at the International Conference on Computer Communications (Infocom) in 2020, for his contributions to information security. In 2022, he was elected as a Fellow of the Institute of Electrical and Electronics Engineers (IEEE) for his outstanding work with information and network security.
Outside of his research, Yu serves as a faculty advisory council member, a Schaefer School of Engineering and Science doctoral committee member and co-chair of the electrical and computer engineering Ph.D. program. He also teaches undergraduate and graduate classes and supervises students working on their doctoral degrees.
Yu strives to inspire and encourage each student’s unique interests and urges them to team up, which he said allows them to “see the bigger picture.”
“Students have different backgrounds and stay with the school for different periods of time, so they’re different in the way they learn, and they have their own paths,” he said
“I’m always proud of my students,” Yu added. “Some of them have overcome a lot, and I can remember every student’s journey.”
While Yu has been teaching for six years at Stevens, his approach to teaching, he said, is continuously evolving.
“I’m always learning to be a professor,” Yu said. “I love working with students to maximize their work, and, if they make mistakes, working with them to overcome those challenges. It’s exciting to witness their growth.”
The students, he said, help him grow as well.
“I'm happy to share my research, which is useful preparation for their own paths,” Yu said. “And sometimes, as they think about it, they will look at things differently and suggest new ways of approaching a problem I’m working on. Being part of that process is very rewarding for me, too.”